DNS Zone Transfer Attacks
Essentially enumeration of valid domains and subdomains as well as further information in them.
This isnt strictly related to the web as it covers the DNS protocol. However, being able to interact with a DNS server opens a potential pathway for this attack and is worth knowing.
We could have a domain with multiple subdomains. These are related to virtual hosts when these are handled by the web server (as in the HTTP protocol). If you can access different web applications pointing to the same server (IP) then we're dealing with virtual hosts. These will be present in the host header within HTTP requests.
- oscp.exam
- dev.oscp.exam
- prod.oscp.exam
- mail.oscp.exam
- secret.oscp.exam
Alternatively, DNS can be used to handle domains and subdomains. In a DNS zone transfer, thanks to the DNS protocol, there'll be other information enclosed in these hosts. Such as domain/subdomain names, IPs, TXT files, etc.
HTTP will map each domain and subdomain to a separate vhost, registered by the web server (e.g. nginx). While DNS maps each string to a domain, address or TXT file. If you perform a zone transfer with the DNS service on a machine, you ask the DNS server to give you all the entries associated with a zone. If it's misconfigured then it'll not ask for credentials and will just give you the zone. It's not supposed to just tell you about all the existing subdomains/domains associated with it..
This means we can enumerate virtual hosts much more efficiently with this. Something like gobuster might not pick up very custom subdomains, is slower and relies on HTTP requests.
Dig
Request all the zones
dig axfr oscp.exam @IP
As an example, this vulnerable DNS server has given over it's subdomains. Highly insecure and we shouldn't be able to do it.
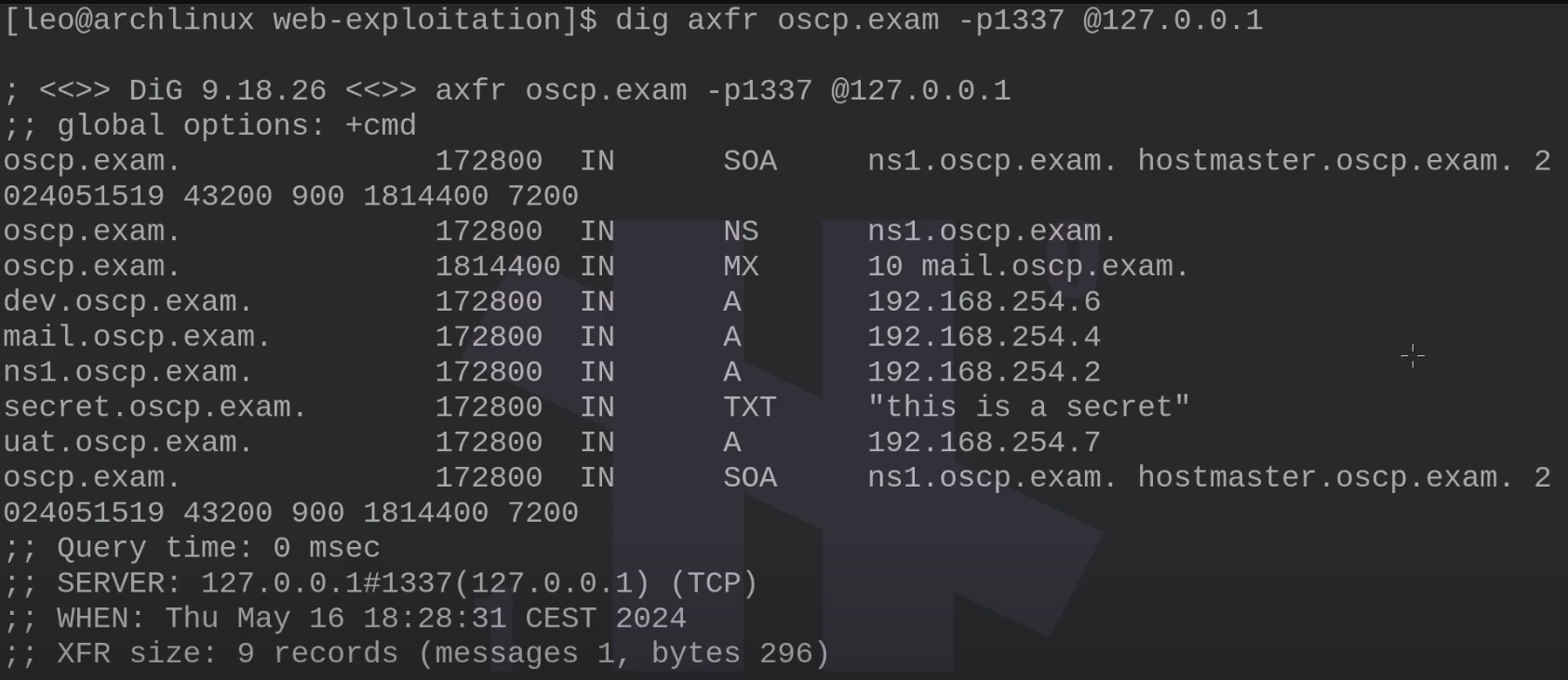
Note the different record types stored (SOA, MX, A, etc)
- SOA determines the configuration of the DNS.
- A records tell you what domain name is mapped to what IP address, this is what gives us the available domains directly.
- ns1 subdomain is another DNS domain. Interesting.
- We also have a TXT document, highlighting how data disclosure can happen here.
Now we know about the available internal IP addresses.
Browser will:
1. Do a DNS query to get the address of the server
2. Uses the same domain value to perform a virtual host query with the HTTP protocol
3. Domain as DNS value -> Domain as Vhost value -> Connect to Vhost
If there is a vhost on dev.oscp.exam with a web application on it; the browser will complete the above to serve up the correct web resources.